This article details the configuration of user credentials and security permissions, the reader of this article should have read the Pulse Security and Pulse Group Security articles.
User Security
The credentials for a client to login into the application are defined by user. A User can be associated to one or more groups. The users are defined under Administration -> Users

Only an Administrator or a User with access to the “View/Edit Users” role will have access to create, modify and delete users.

Create a User
-
Go to Administration – > Users in the Pulse Web client
-
Click in “Add Button”
Enter the Cognos Namespace in the case you want to use CAM Security, More details read Configuring Pulse with CAM Security and How to Configure Users to Login with their CAM Credentials articles.
-
Enter a name in the Name of the User
-
Enter a Password, the robustness of the password can be set in the Pulse.cfg file please refer to the “How to specify the password robustness policy” section in this article form more details
-
Select if the user is going to be an Admin: An Admin user will have access to all Pulse features and all the instances
-
Select the groups to which the user will be a part of
-
Click in the save button
Delete a User
-
Go to Administration – > Users in the Pulse Web Client
-
Click in the name of the user in the left side pane
-
Click in the Delete button
-
A Confirm message will pop up, select OK to confirm
Modify a User
-
Go to Administration – > Users in the Pulse Web Client
-
Click in the name of the user in the left side pane
-
Perform the desired changes
-
Click in the save button
About the Admin User
The admin user is created during the installation of the product, the Admin user cannot be deleted, a reset of the password can be performed by following these steps in this article.
How to specify the password robustness policy
The password robustness policy is controlled by the “Validation” parameter in the Pulse.cfg file, this is performed by setting a regular expression that will be used by pulse to evaluate the complexity of the passwords that are being set for the users.
As default any user password (unless CAM Security is going to be used for the user) has to be at lest 8 characters long with at least 1 number, 1 upper case, 1 lower case and a special character.
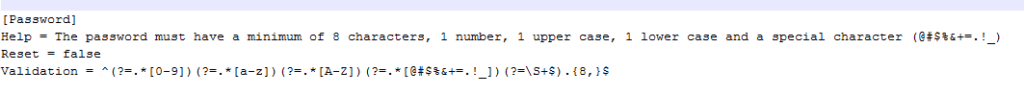
This validation parameter can be changed as follows:
-
Open the <Pulse Installation Path>confgPulse.cfg file
-
Under the Password Block set a Valid Regular expression, if a blank value is set, the validation of the password will be avoided
-
Restart the Pulse services