This article details the Group security, the reader of this article should have read the Pulse Security article.
Defining Groups in Pulse
The Groups are entities that define the security in the application for a given user or a set of users. These groups are defined under the Administration -> Groups.

Only an Administrator or a User with access to the “View/Edit Users” role will have access to create, modify and delete groups.
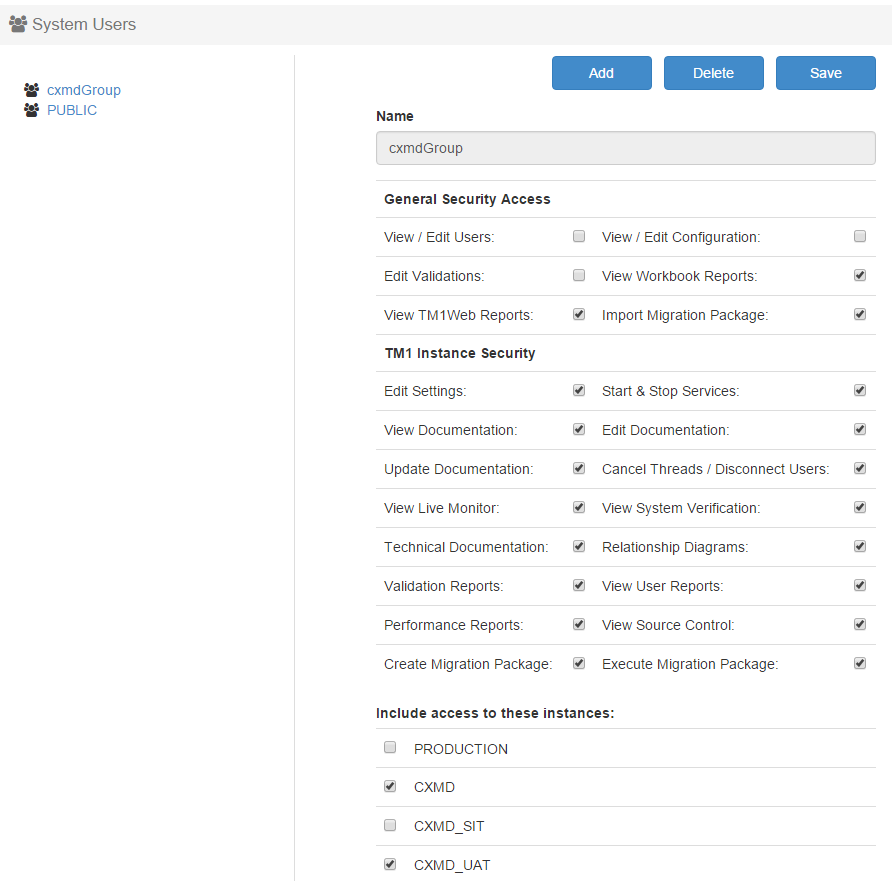
Creating Groups
-
Go to Administration – > Groups in the Pulse Web client
-
Click in “Add Button”
-
Enter a name in the Name text box
-
Select the permissions that will be given to the group
Select the “Instances to Exclude” or “Instances to include” access for the users. See: Configuring Pulse Security to Exclude or Include Instances
-
Click in the Save button
Deleting Groups
-
Go to Administration – > Groups in the Pulse Web Client
-
Click in the name of the group in the left side pane
-
Click in the Delete button
-
A Confirm message will pop up, select OK to confirm
Modify a Group
-
Go to Administration – > Groups in the Pulse Web Client
-
Click in the name of the group in the left side pane
-
Perform the changes in permissions and/or instance access
-
Click in the Save Button
About the Public Group
A “Public” group is crated when Pulse is installed for the first time, and it cannot be deleted but it can be modified, all the users will be members of the public group.
What to do next?
Pulse User Security